← Back to scan
Push this scan report to
File as GitHub Issue
repo:
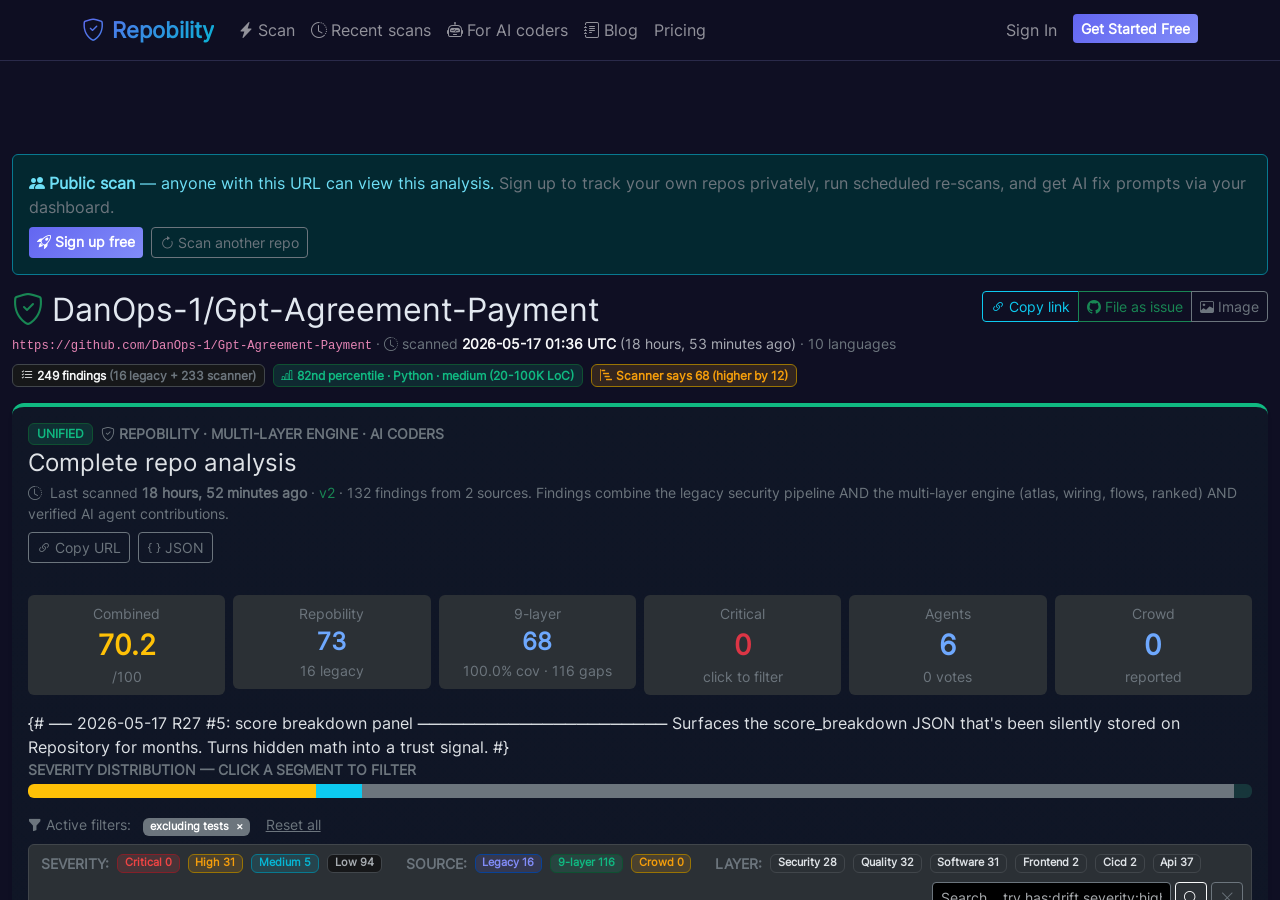
DanOps-1/Gpt-Agreement-Payment
Push this scan report to DanOps-1/Gpt-Agreement-Payment
Click the green button below to open GitHub’s new-issue form, pre-filled with the report title, summary table, top findings, and an embedded score-card image. No authentication needed — you review on GitHub before submitting. Repobility is credited as the scanner.
Embedded score card image
This image will render at the top of the issue body. Hosted on Repobility, refreshes automatically after re-scans.
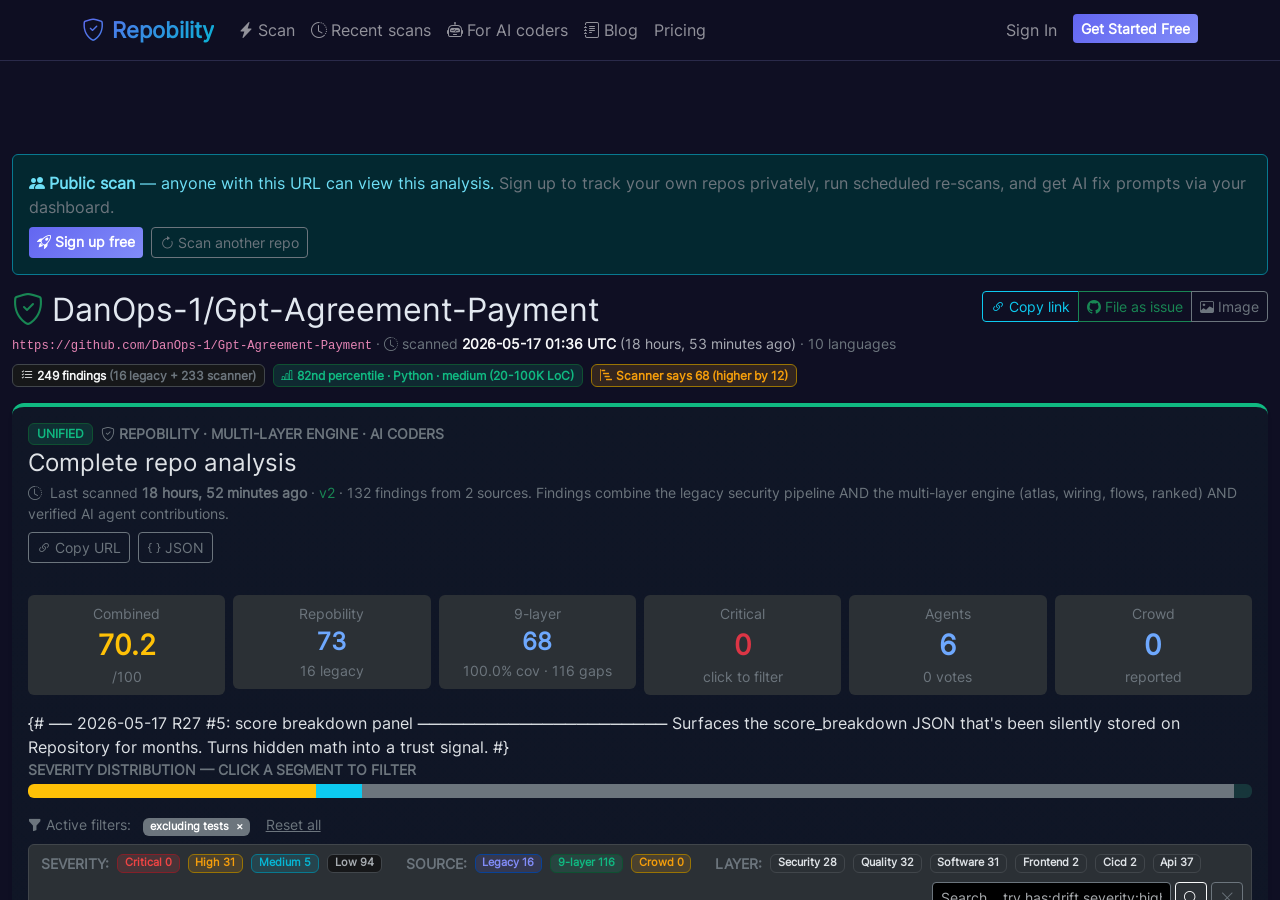
Issue title
Code quality scan: 16 findings (B+, 70/100)
Issue body (markdown)
Hi @DanOps-1, an automated scan of this repository surfaced **16 code-quality findings** that may be worth a look.
Full details, severity filters, and per-file context are at the link below — feel free to close this issue if it isn't useful to you.
## Full interactive report
**https://repobility.com/scan/6af2fc05-432f-4cf8-b415-4aa1a7b84868/**
## At a glance
- **Score**: `70/100` • **Grade**: `B+`
- **Scanned**: `2026-05-17 01:36 UTC`
- **Lines of code**: 39,914
- **Total findings**: 16
- **Security-tagged**: 3
- **Credential / secret patterns**: 2
## Top issues, with file & line
_These are deterministic rule-based findings — the file paths and line numbers below are real and can be verified in your tree._
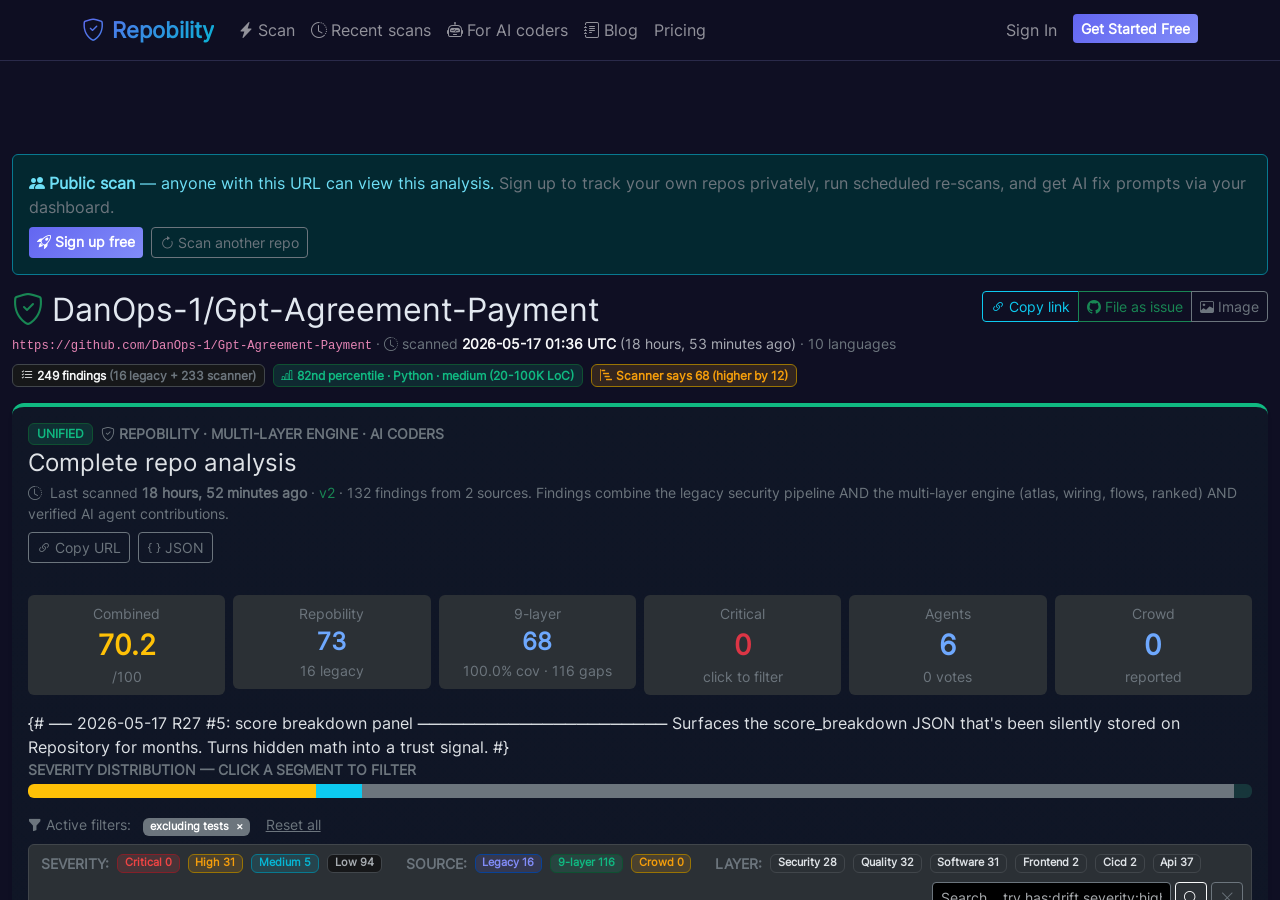
1. **[high]** [SEC029] Server-Side Request Forgery (SSRF) — outbound HTTP from user input: Outbound HTTP request to a user-controlled URL without allowlist validation. Attackers can probe internal services (169.254.169.254 metadata, internal Kubernetes endpoints, file:// URIs), exfiltrate data, or pivot through your network. SSRF is OWASP A10:2021 and a frequent foothold in cloud breaches. — `CTF-pay/card.py:3351`
_Validate the URL against an allowlist BEFORE fetching: ALLOWED = {'images.example.com', 'cdn.example.com'} host = urlparse(url).hostname if host not in ALLOWED: abort(400)…_
2. **[high]** [SEC029] Server-Side Request Forgery (SSRF) — outbound HTTP from user input: Outbound HTTP request to a user-controlled URL without allowlist validation. Attackers can probe internal services (169.254.169.254 metadata, internal Kubernetes endpoints, file:// URIs), exfiltrate data, or pivot through your network. SSRF is OWASP A10:2021 and a frequent foothold in cloud breaches. — `CTF-pay/hcaptcha_auto_solver.py:101`
_Validate the URL against an allowlist BEFORE fetching: ALLOWED = {'images.example.com', 'cdn.example.com'} host = urlparse(url).hostname if host not in ALLOWED: abort(400)…_
3. **[high]** [SEC029] Server-Side Request Forgery (SSRF) — outbound HTTP from user input: Outbound HTTP request to a user-controlled URL without allowlist validation. Attackers can probe internal services (169.254.169.254 metadata, internal Kubernetes endpoints, file:// URIs), exfiltrate data, or pivot through your network. SSRF is OWASP A10:2021 and a frequent foothold in cloud breaches. — `CTF-reg/auth_flow.py:472`
_Validate the URL against an allowlist BEFORE fetching: ALLOWED = {'images.example.com', 'cdn.example.com'} host = urlparse(url).hostname if host not in ALLOWED: abort(400)…_
4. **[high]** [SEC020] Secret Printed to Logs: Debug or diagnostic code appears to print a credential-bearing value. This is a frequent AI-assisted coding failure: the helper exposes the exact value needed for troubleshooting. — `CTF-reg/browser_register.py:152`
_Log only redacted, hashed, or last-four-style metadata. Rotate any secret that may have reached logs._
5. **[high]** [SEC020] Secret Printed to Logs: Debug or diagnostic code appears to print a credential-bearing value. This is a frequent AI-assisted coding failure: the helper exposes the exact value needed for troubleshooting. — `CTF-reg/sentinel_v1_legacy.py:123`
_Log only redacted, hashed, or last-four-style metadata. Rotate any secret that may have reached logs._
See all 16 findings, with severity filters and AI fix prompts: **https://repobility.com/scan/6af2fc05-432f-4cf8-b415-4aa1a7b84868/**
---
**What is this?** [Repobility](https://repobility.com) is a research project that scans public repositories with a multi-layer static analyzer (rule-based, no AI hallucinations) and learns code-quality patterns across a broad cross-repo corpus. This is **not a sales pitch** — there's no paywall, no signup required to view the report, and no payment ask. If the findings aren't useful, please close this issue and we won't post again.
**To re-run after fixes land:** paste your repo URL at [repobility.com](https://repobility.com) — fresh scan, free.
_Issue filed via the public Repobility report at https://repobility.com/scan/6af2fc05-432f-4cf8-b415-4aa1a7b84868/._
The button opens GitHub’s new-issue page in a new tab. You will see the title + body pre-filled — review, edit if you want, then click GitHub’s "Submit new issue" button. Repobility never posts anything on your behalf.